One of globalization’s many effects has been the creation of IT outsourcing, and the rise of countries such as India as global players in IT services. Extending networks out into cyberspace has given rise to the need and the possibility for machines to be remotely controlled, whether you’re speaking about domotics (remotely controlling the temperature or lighting of your home while you’re away, for example), or fixing a bug on a machine on another continent.
Companies now have their resources, IT and otherwise, geographically distributed; in different branches or offices, subcontracted in the Cloud, and using local or global support services. Pandora FMS is right there, in this global mix of interconnected, and isolated networks, contributing technological solutions to global business/tech issues with new features and functions, including the sync server on the latest version of the flexible monitoring tool Pandora FMS version 7 “Next Generation”.
The sync server has been designed in response to demands for monitoring secure isolated environments without outgoing connections. These restrictions mean that communication must be initiated from an external network. This is an important distinction as a bidirectional open network can employ a satellite server or a proxy without any problem.
Definition
The sync server system consists of deploying the monitoring park to isolated networks that are unable to communicate for themselves with the main Pandora FMS server or the MySQL database.
This function allows software agents to be deployed and to carry out network checks against remote networks that are isolated from the Pandora FMS central server. Install a connection point for the Pandora FMS central server to collect the information from the isolated network. This will be the only via of communication. The rest of the network will remain secure and isolated and won’t need to initiate communications to the outside.
Imagine you have two datacenters in two different countries, one in Europe, the other in Asia. Both are secured, and communications are impossible from the Asian office, due to the danger of cyber-attack communications are impossible from the Asian office to the Pandora FMS server in Europe. Since the server monitor has access to sensitive material, we’ll use this function so that all communications are initiated from the Pandora FMS server in Europe.
Another possibility is to maintain a DMZ under monitoring to make sure that no connections are made between this network and your internal network. Doing this will increase security, avoiding man in the middle and network poisoning attacks.
This extension of monitoring practice, irrespective of localization and achieving security offers a new and powerful possibility for scaling your monitoring.
Monitoring isolated networks can be performed in combination with a satellite server and proxy and broker modes with Pandora FMS agents thanks to the sync server’s potential to combine with other functions.
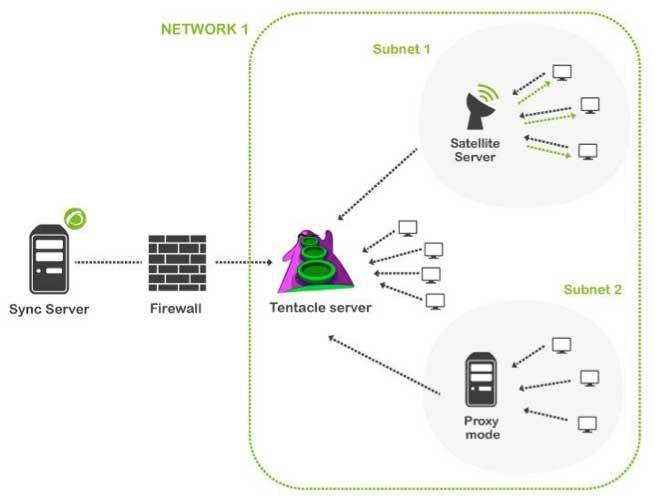
The above outline shows an example of a distributed environment that could be monitored combining various Pandora FMS functions. The possibilities are endless when it comes to adapting to different topologies.
Operational overview
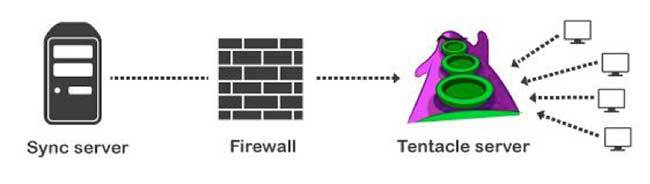
On the remote network, a tentacle server is installed as a communication point, which will also receive the information from software agents installed on your network devices. You can install a satellite server at the same node to execute remote checks against any network device.
All data can be transferred to the Pandora FMS central server via this communication point as soon as it initiates a connection and recovers the information collected since the last time the connection was made.
The particularity of the sync server’s operational modus operandi, as distinct from the satellite server or a Tentacle proxy, is that communications are always initiated from the Pandora FMS server, and neither outgoing communications or the sending of packets from the remote network is permitted.
Configuration
Before getting on to configuration, make sure that both the Pandora FMS server and the Tentacle server installed on the network are updated to version 7 of Pandora FMS.
On the Pandora FMS server modify the pandora_server.conf file with the following parameters:
syncserver 1
sync_address
sync_port
And in the remote Tentacle server start up script add only the two parameters “-I –o”:
TENTACLE_EXT:OPTS="-i.*\.conf:conf;.*\.md5:md5;.*\.zip:collections -I -o"
The sync server environment also supports secure SSL communications; in order to configure this, add some additional parameters to the previously mentioned files.
In pandora_server.conf:
sync_ca /home/cacert.pem
sync_cert /home/tentaclecert.pem
sync_key /home/tentaclekey.pem
In the Tentacle startup script tentacle_serverd (on one line):
TENTACLE_EXT_OPTS="-i.*\.conf:conf;.*\.md5:md5;.*\.zip:collections -e /home/tentaclecert.pem -k /home/tentaclekey.pem -f /home/cacert.pem"
About Pandora FMS
Pandora FMS is a flexible monitoring system, capable of monitoring devices, infrastructures, applications, services and business processes.
Of course, one of the things that Pandora FMS can control is the hard disks of your computers.
Would you like to know more about what Pandora FMS can offer you? Discover it by entering here: https://pandorafms.com
If you have more than 100 devices to monitor, you can contact us through the following form: https://pandorafms.com/en/contact/
Also, remember that if your monitoring needs are more limited you have at your disposal the OpenSource version of Pandora FMS. Find more information here: https://pandorafms.org
Do not hesitate to send us your queries. The Pandora FMS team will be happy to assist you!
Pandora FMS’s editorial team is made up of a group of writers and IT professionals with one thing in common: their passion for computer system monitoring. Pandora FMS’s editorial team is made up of a group of writers and IT professionals with one thing in common: their passion for computer system monitoring.




















